10 Pointer Web/Mobile App Security Checklist to Enable Uninterrupted Business Growth
An ordinary day in the life of a smartphone user begins and ends with mobile apps. Whether they want to know the latest news, and weather updates, connect with friends, or shop for groceries, they go to an app.
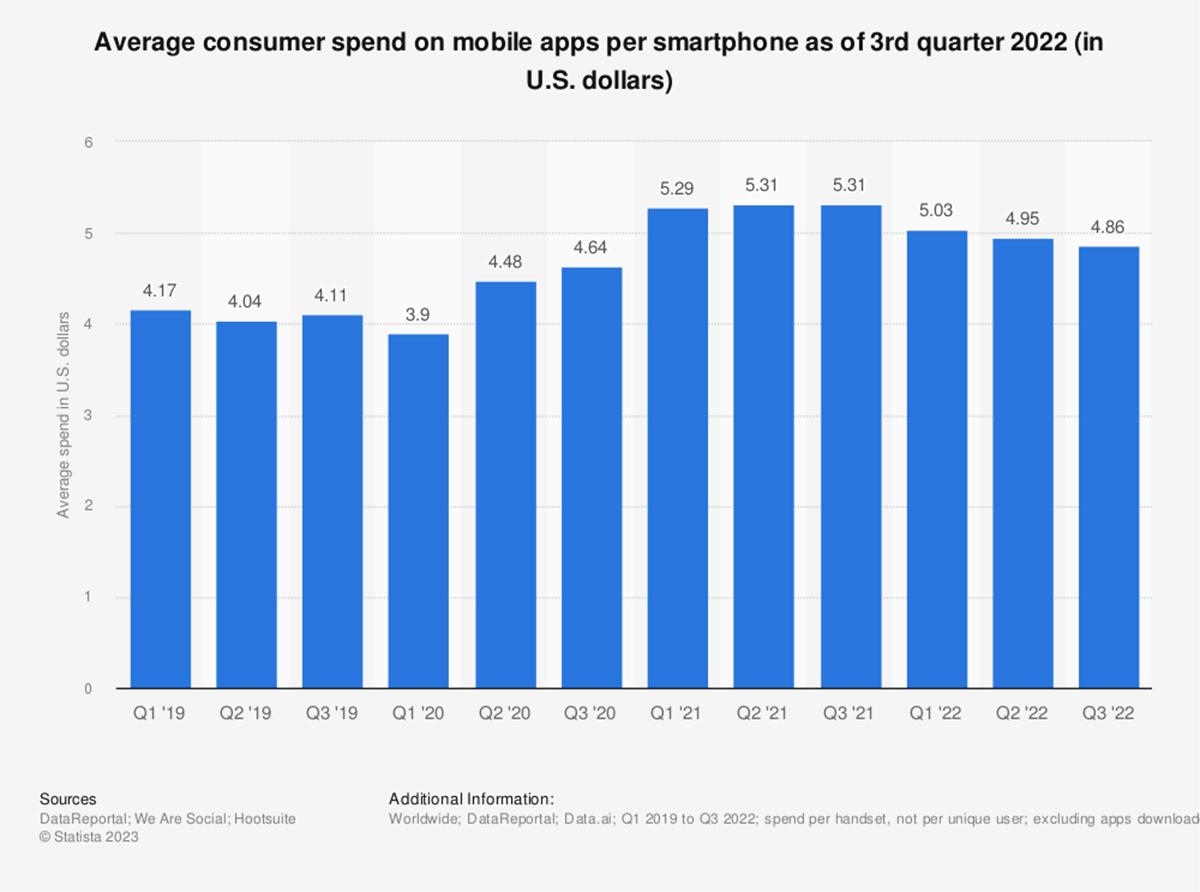
The monumental rise in web and mobile applications support, especially in the post-Covid era, has led to increased user efficiency and convenience. The average customer spending on mobile apps is an indication of increased mobile usage (Statista).
While many advantages are associated with the mobile application, it is also the gateway to fraud. As shown in the graph, Cybercrime is estimated to increase by multi-folds by 2027 (Statista).
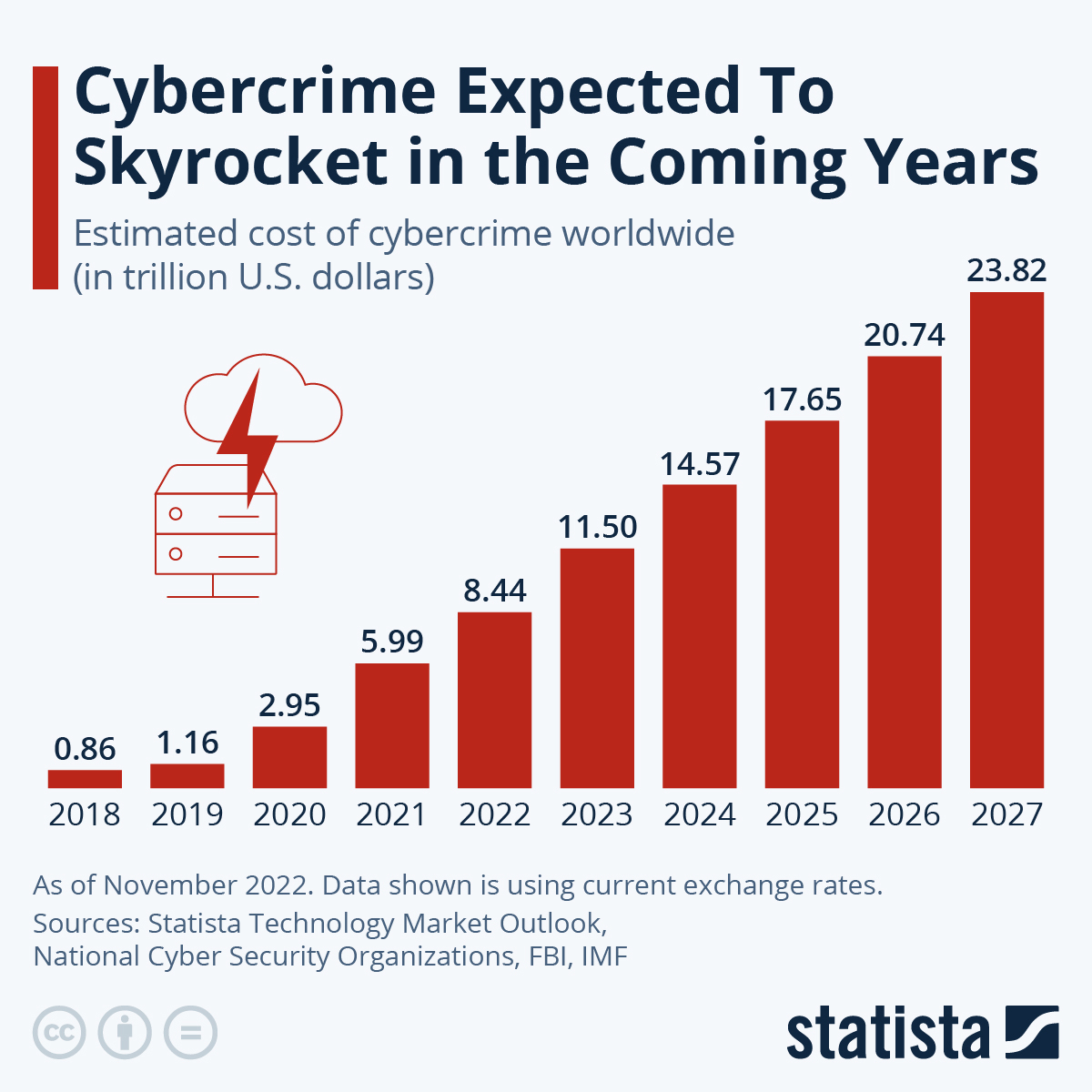
The most popular types of fraud include SDK Proofing, Click Injection, and Click Spam. At least 38.7% of app installs were rejected owing to fraudulent activities.
Mobile app security is an important investment for businesses planning to overcome fraud and enhance app usability. The security enhancements should be vetted so that you experience no data leaks and improve the authentication. It will ensure you transmit data after fully encrypting it for better protection.
This guide will take you through the web and mobile app security checklist, best practices to enhance security, and tools you need to implement.
What is App Security?
Mobile application security is the way to improve user data or code to ensure reduced risk-free access and better data management. It comprises the design and development of the security architecture that helps systems move data and collaborate for seamlessness in processes to ensure protected applications.
Role-based access, routers that ensure the IP addresses are not visible, encrypted data transfers, etc., are all ways to improve security. In the application, the security is bound to the firewall, which ensures better protection and restricted access.
Every application needs full-fledged and completely defined security measures. Here’s a mobile application security testing checklist that will help you deliver a secure mobile app.
10-Point Mobile Application Security Testing Checklist to Secure Your Apps
To ensure you have secured the application, you can use this checklist to go through your app once. It will help to know if you have included the security requirements or not.

#1 Implement Code Signing Certificate
The code signing certificate is a great way to ensure that the source code you have received is devoid of malware or third-party alterations. Most hackers love to implement malware in open-source software solutions.
When developers use this source code, it leads to malicious mobile or web applications. With a code signing certificate, you can guarantee that the source is free of security threats. Developers and source code owners need to use popular code signing certificates such as Symantec certificate, Comodo, and Sectigo in the source code.
#2 Encode Your Mobile Communication
Several threats are looming over your mobile app. For instance, the man-in-the-middle attack that takes place over WiFi can lead to data threats and extreme app risks. Similarly, if you leave the conversation between the mobile app and the servers open, several networks are vulnerable, leading to malware attacks.
To avoid these, you might want to encrypt the data transfer between the mobile app and the respective servers. Implementing session-based key exchanges or using the 4096-bit SSL key can reduce the vulnerabilities.
It is equally important to protect the data stored within mobile phones by encrypting it. It is possible that certain mobile apps don’t allow customers to download sensitive data.
#3 Provide Multi-Factor Authentication
Instead of opting for multiple checks and authentications that can disturb the customer’s experience on the application, you can install two-factor authentication at the start. This will ensure proper security and minimal friction in usage.
A combination of pin and biometrics or other methods to get the user to enter the application will improve the experience. The path to success often looks intimidating, but the rewards are extraordinary! With your program set up, you can bypass the tedious authentication process and jump straight into using it.
The effort of the initial setup may seem like a big hurdle to overcome, but it's worth it in the end. You no longer have to go through the tedious and time-consuming process of authentication every single time you want to use your program - now that's something to be thankful for!That's a reward worth striving for. That's a reward worth striving for.
#4 Opt for Pen Testing
This is one of the best things to do to improve the security of your mobile application, according to the mobile app security checklist. It helps you determine the security of your application.
You will know what vulnerabilities exist in your app from the hacker’s perspective. It allows the human eye to detect inaccuracies, vulnerabilities, and issues/bugs. A few common issues you can decipher and remove with pen testing include checking if the password policy is perfect, data encryption, and deciphering issues with third-party permissions.
#5 Secure the APIs
When you want to engage with third-party libraries or wish to enhance communication between apps, you use the APIs. Most SaaS products are devised using multiple APIs, as it is a cost-effective way to introduce multiple features.
However, this integration can cost you security. It is important to secure the APIs before using them for the application so that data transactions are secure. It is equally important to conduct thorough API testing to decipher the data access authorizations available.
#6 Incorporate the Runtime Application Self-Protection
When increasing the security of your mobile apps, the RASP tools play a pivotal role. They can ensure that no malicious or dangerous actions take place while you are compiling or running the app in a production environment. These tools will ensure that app executes the defined behavior at the end.
In case you notice malicious activity during runtime, you can call the database and check for issues within. These tools can protect the apps and ensure they aren’t vulnerable to SQL injection, cross-site scripting, or other attacks.
#7 Install the Tamper Detection Tools
Identifying if the app has been tampered with during the early stages is important for businesses. It can help remove wrong code and ensure you have added the perfectly curated code for the application.
Some tools and technologies help detect if someone has tampered with the code you are using. These tools can also detect if there have been slight changes in the app. Several strategies help with tamper detection, including alteration in Java bytecode, binary patching, and code injection. These detect the malicious code in the early stages, thus preventing further app issues.
#8 Avoid Personal Devices in Offices
While BYOD can attract low cost and is technically the best way to operate for small and medium businesses, it has its issues. If the device is Jailbroken, the security restrictions aren’t too many.
As a result, it can impact the security of the application built on such devices. If developers or testers use such devices to build/test/deploy apps, the apps can contain malware. Eventually, it can also lead to the rejection of the apps at the app store.
Instead of allowing the user’s device, you can make them use the company’s devices. If you plan to implement BYOD, ensure maximum security within the policies and mobile devices.
#9 Avert the Data Leaks
It is important to ensure that business apps are separate from personal ones. This will ensure that the data from the personal apps don’t lead to data leaks from within the business apps. It will protect workplace solutions from getting attacked by malware. It will also minimize the risk associated with data storage and loss of sensitive data.
A few ways to avoid data leaks include using user timestamps on the susceptible files and preventing the clipboard from copying the username/password.
#10 Policies to Prevent Device Theft
Your device is your bank, shopping center, and everything else. Your apps contain all sensitive information. You cannot lose your smartphone, as everything sensitive is stored within.
However, if you ever lose your device, it should be protected to ensure sensitive data isn’t leaked. Ensure to include a code that allows you to wipe out things from the phone once they reach the wrong hands. It is a good idea to avoid storing sensitive information on mobile.
6 Best Practices to Ensure Secure Web/Mobile Apps
When you incorporate the mobile application security checklist, you can avoid the pitfalls and ensure better app deployments. However, if you implement these best practices, you can launch a bug-free app. You won’t face pitfalls or inaccuracies within the app, as you will handle them during the development stage.

#1 Incorporate the DevSecOps Approach
The DevOps approach tends to bring collaboration between the development and security teams. DevSecOps extends this collaboration to the security of the mobile app too. It will help the developers identify and fix security issues during the development phase.
With this approach, the developers and testers, strategists, and operations experts can view the security issues along the different stages of software development and correct them immediately.
#2 Automate Security Tasks
Several tasks are manual and repetitive. You can create an algorithm to ensure that these tasks are automated and happen at the speed you expect. This will help the security teams to focus on more important and high-priority tasks. This will make the security team productive.
#3 Assess the Risks
A complete risk assessment will help determine your potential issues with the mobile application. It should be conducted as part of mobile app security best practices. For instance, the assessment will help you realize the assets that need immediate protection.
Check the potential threats looming upon your application and determine ways to isolate them. Similarly, check how to implement the right security measures and detect attacks in the future. During this phase, you will also need to plan for the infrastructure, such as tools and resources.
#4 Role Management and Access Control
This is an incredible way to incorporate security while planning your mobile application. Do not allow everyone to access mobile applications or control the data. You should offer specific controls based on their roles in the company and level within the hierarchy.
Additionally, implement a strong password into the application. You can use robust recovery methods that can increase the app's security. Multi-factor authentication is a great way to ensure maximum role-based access and a thoroughly secure application.
#5 Implement Patches Periodically
You should implement patches during app maintenance to avoid ruining your software by not keeping the operating system or source code updated. Conduct these regularly to assure maximum security as per the mobile app security best practices. It can also help provide solutions to the problems that exist within the application. You can also resolve things like compatibility issues or app architecture problems with these patches.
#6 Adhere to Compliances and Protocols
When developing an application, ensure to include the compliances and protocols within the policies. This can enhance the security of the app you could use the design guidelines, data protection methods, and others to improve the security of the mobile app use the proper and reputed code signing protocol to secure the source code.
Top 5 Tools for Mobile App Security Testing
Tools can save a lot of the time that goes into developing security guidelines, implementing them, and testing the solution. Here are a few tools that can help automate Mobile App security testing.

1. Qark
Keep your app secure and discover issues early with LinkedIn's Quick Android Review Kit (QARK). By detecting tampering in the source code, QARK will help you identify bugs and get them fixed before they can become a problem. Keep your app safe and running smoothly with QARK! It gives you a clear and concise report on the issues with the web or mobile application.
2. MicroFocus
The MicroFocus tool was devised to help conduct end-to-end security testing. It is a platform-agnostic tool and checks the app on multiple devices. It helps determine the security inaccuracies across web, desktop, and mobile platforms. You can also detect malware using this tool.
3. Android Debug Bridge
This command line tool allows you to connect the app across multiple Android devices and check for security issues. You can monitor the events in real time. You can also check for networking-related issues within the application.
4. Synopsys
It is one of the finest tools used for application security testing. It will check for vulnerabilities from the hacker’s perspective. You can address the app's third-party code issues and security problems during the early phases of SDLC.
5. AppScan
This security testing tool developed by HCL is used to test and monitor the security policies and guidelines for web and mobile apps. It offers SAST, DAST, and risk management strategies for security testing. It can crawl the app to be tested and check for vulnerabilities. It will give the developers a heads-up on the security situation.
Conclusion
Application security is an integral part of app development. It involves ensuring your app is free of issues and examining the app for future vulnerabilities. Checking the app from a hacker’s perspective is one of the best strategies to improve app security.
Implementing the mobile app security checklist while conducting a security check of the application can help you determine the bugs and remove them before deployment. However, incorporating the best practices can ensure you are deploying a bug-free and high-quality app it will minimize the app risks and enhance the testing efficiency.
Expert App Devs is a web and mobile app development company that offers end-to-end mobile application security testing solutions. Connect with our team to develop a secure app. We also offer core app security testing solutions.
 Ninkal Munjani
Ninkal Munjani